There was a recent arrest of a 19 year old in Halifax for “hacking” freedom-of-information releases from a government website. Alleging he is guilty of section 342.1 of the criminal code, which prohibits unauthorized uses of computers “with intent to commit an offence.”, maximum penalty 10 years jail. I have seen a lot of confusion about what he actually did, the actual news story can be best read about here at the Global News here and the CBC here, and a few legal precedents are covered by Troy Hunt (an expert in the field) here. But what did he actually do? I’ll try to explain, let’s say I publish a list of pages for you to view:
https://300m.com/page_1.html
https://300m.com/page_2.html
https://300m.com/page_4.html
https://300m.com/page_5.html
You might notice a gap, you might think I forgot to provide the link, you might assume the link is somewhere else, maybe the 3rd page just does not exist, checking if it does or what it contains by editing the website address in the browsers address bar, changing this:
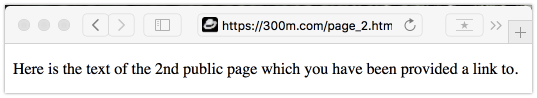
into this: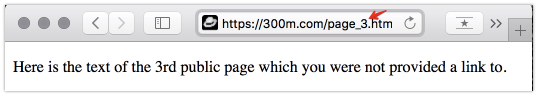
that is the crime this kid has been accused of.
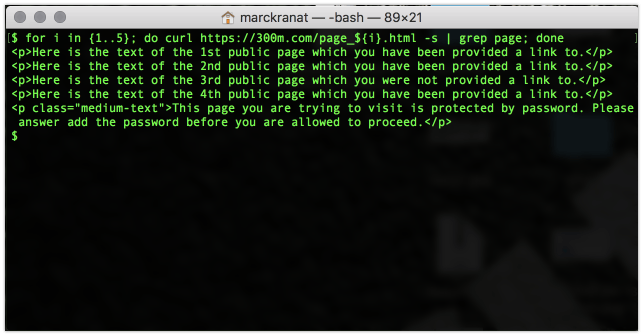
But he automated these requests, I would guess he used the tool wget to enumerate the public pages, maybe he was just lazy, that’s why I do this everyday to grab long lists of web pages, I use cURL, specifically to grab a list of pages and their content. Using something similar to this in my Terminal:
$ for i in {1..5}; do curl https://300m.com/page_${i}.html -s | grep page; done
and I’ll get something like this, the contents of 4 pages in one go:

You might notice, that /page_5.html, even though I provided a link above, but you were blocked, but I authorize you to read that page, just you of course, using the passcode: 3Q3l9rVuNtOqgM.
So someone visiting that page from either a link, or through such a method as the enumeration above, can see this is a blocked resource, trying to access that resource without being legitimately provided a passcode, that would clearly be criminal. Enumeration of publicly available resources using such tools, with no malicious intent, as I and anyone else in technical support, system management or cyber security do daily, just as this kid did, could never be criminal. The second you use any publicly available resource for a crime, you are a criminal.
What I would consider should be investigated in this case though, is the leaving of potentially harmful (by the local authorities own admission) personal private data wide open on publicly accessible web pages, security through obscurity (not linking to in this case) never works, is not real security, and is in the security industry always considered bad practice. There should have been some authentication, such as my passcode, at a bare minimum.
And another thing, if you tried to crawl my site in this way (using cURL or wget) too aggressively, say anything more than 50 requests, the automated IDS (intrusion detection system) would fully block you, that’s just good practice, 7000? I guess it’s lucky for them the tax payer pays for their resources. There is nothing wrong requesting a large amount of data using tools such as this, it is done all the time, if a site owner does not like that behaviour, the burden is on them to limit it.
My personal guess would be here, on the information provided, that staff are desperately trying to deflect attention from their own incompetence in managing IT security.
This has ended in the best of all possible results. The charges have been dropped. My thanks to all that donated and the police investigation that concluded in a just manner. Awaiting final determination of the legal billing, but I am still recommending that any of the generosity that you folks have shown left over as a remainder be applied to a tuition scholarship for this young man’s continuing education.Test block message: block